Manufacturer Texas Hold'em Lens Hack Scan Card Packs Hiking Playing Cards - Buy Texas Hold'em Playing Cards Lens Hack,Playing Scan Card Packs,Hiking Playing Cards Product on Alibaba.com
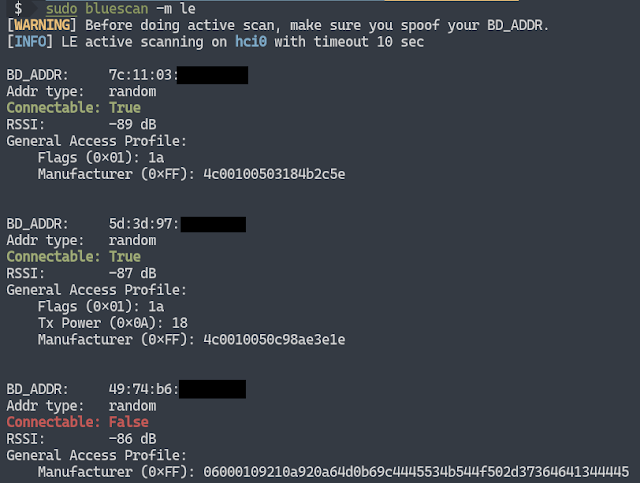
Bluescan - A Powerful Bluetooth Scanner For Scanning BR/LE Devices, LMP, SDP, GATT And Vulnerabilities! - Hacking Land - Hack, Crack and Pentest

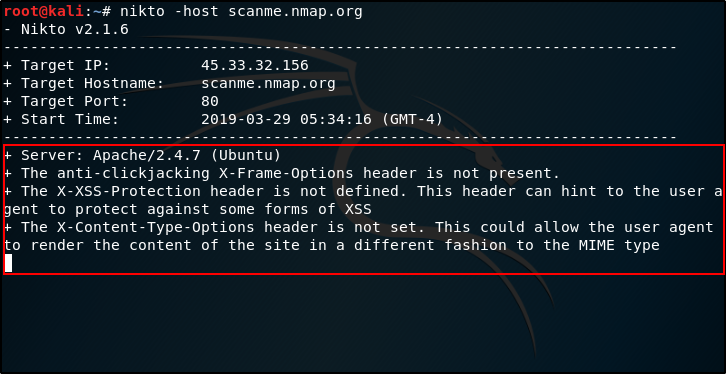
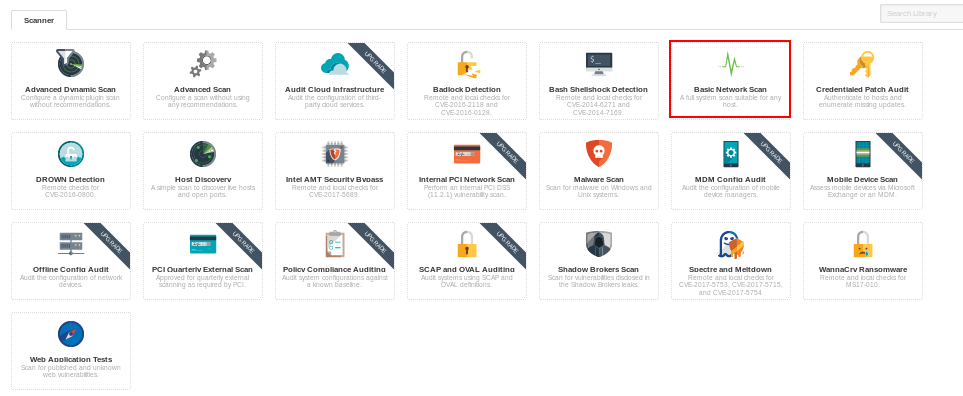
Hack Like a Pro: Using Nexpose to Scan for Network & System Vulnerabilities « Null Byte :: WonderHowTo

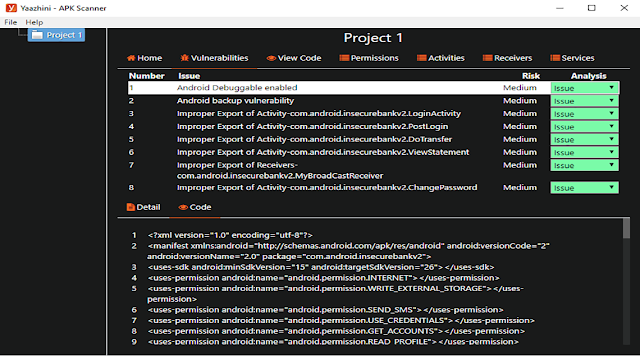
Hack scan wordpress site and supply full hacker vulnerability audit report by Wordpressaudit | Fiverr

Android for Hackers: How to Scan Websites for Vulnerabilities Using an Android Phone Without Root « Null Byte :: WonderHowTo